The Pangu team in China has discovered an "unpatchable" vulnerability in Apple's Secure Enclave Processor that could lead to the compromise of private security key encryption.
This means that the vulnerability exists in hardware rather than software, so devices that have been shipped may not be able to fix the issue.
The Team Pangu has found an “unpatchable” vulnerability on the Secure Enclave Processor (SEP) chip in iPhones. https://t.co/9oJYu3k8M4
— Jin Wook Kim (@wugeej) July 29, 2020
One of the major security enhancements Apple brings to devices is the Secure Enclave Processor, which encrypts and protects all sensitive data stored on the device.
Secure Enclave is a security co-processor included with nearly every Apple device that provides an additional layer of security.
All data stored on iPhone, iPad, Mac, Apple Watch, and other Apple devices is encrypted using random private keys that can only be accessed by the Secure Enclave.
These keys are unique to the device and are never synced with iCloud.
The Secure Enclave not only encrypts files, but also stores keys that manage sensitive data such as passwords, credit card information used by Apple Pay, and even user biometrics.
All of this information can be used to enable Touch ID and Face ID, which makes it easier for hackers to access a user's personal data.
Although the Secure Enclave Processor is built into the device, it works completely separately from the system.
This ensures that applications cannot access the private key, as they can only send requests to decrypt specific data (such as a fingerprint) to unlock the application via the Secure Enclave.
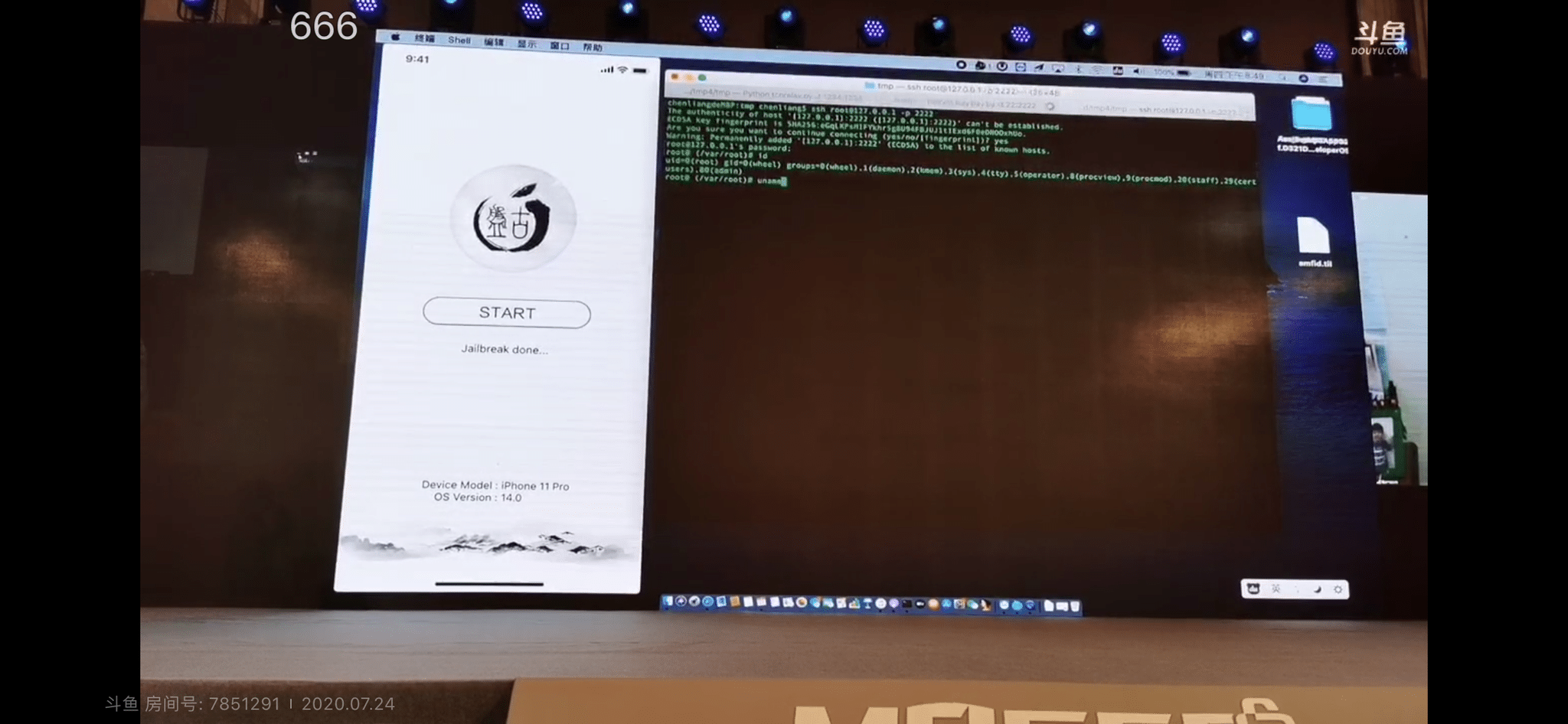
Even if the user is using a jailbroken device with full access to internal system files, all content managed by the Secure Enclave is protected.
Devices equipped with the Secure Enclave Processor:
iPhone 5s and later
iPad (5th generation) and higher.
iPad Air (first generation) and higher.
iPad mini 2 and higher
iPad Pro
Mac computers with T1 or T2 chip
Apple TV HD (4th generation) and higher.
Apple Watch Series 1 and higher
HomePod
This isn't the first time hackers have discovered a vulnerability in Secure Enclave.
Hackers have already been able to decrypt Secure Enclave firmware to explore how the component works back in 2017, except they don't have access to the private key, so there's no risk to users.
But having full access to the Secure Enclave could also mean that hackers could access users' passwords, credit card information, and more.
The only thing that is known about this vulnerability in the Secure Enclave is that it affects all Apple chips between the A7 and A11 Bionic, similar to the checkm8 vulnerability that makes it possible to jailbreak almost any iOS device (including the iPhone X).
Even though Apple has fixed this security flaw using the A12 and A13 Bionic chips, millions of Apple devices running on A11 Bionic or older chips could still be affected by this vulnerability.