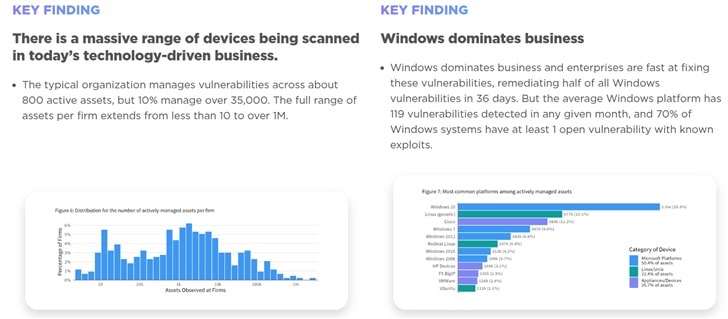
A total of 70 percent of Microsoft's assets have at least one high-risk vulnerability, a recent report said.
The report, authored by the Cyentia Institute, is based on data on Kenna Security's 9 million assets from 450 organizations, and Kenna Security examined the risk profile of Microsoft, Linux, and Mac assets.
Throughout the study period, researchers identified 215 million vulnerabilities in Microsoft assets, of which 179 million, or 83 percent, had been fixed.
According to Kenna Security, the remaining 36 million unpatched vulnerabilities are higher than the combined Max, Linux, and Unix assets.
Microsoft also has the highest percentage of closed, high-risk vulnerabilities at 83 percent. This is closely followed by Apple OSX, followed by Linux/Unix and network devices/IoT devices. In addition, 40 percent of Linux and Unix assets and 30 percent of network devices have known vulnerabilities.
However, Kenna Security also points out that fewer vulnerabilities don't necessarily mean a device is more secure.
In a world where a single high-risk vulnerability can have catastrophic consequences, effective patch prioritization and speed are key to security, independent of the device or software type.
Although Microsoft has more vulnerabilities than others, this does not necessarily mean that it is at total risk, as Microsoft can also fix vulnerabilities faster.
The report found that Windows-based assets have an average of 119 vulnerabilities per month and that these are patched every 36 days on average.
This compares to an average of only 3.6 vulnerabilities per month for network devices, but these vulnerabilities take about a year to fix.
Apple had the second-highest patch rate at 79 percent, while Linux, Unix, and other network devices had a 66 percent patch rate.
Wade Baker, Partner, and Founder of the Cyentia Institute said, "With automated patching and 'Patch Tuesdays,' Microsoft has been able to fix critical vulnerabilities on its systems at a remarkable rate, but it still has many vulnerabilities. "On the other hand, we see many assets, such as routers and printers, that have a longer shelf life for their high-risk vulnerabilities. Companies need to align their risk tolerance, strategy, and vulnerability management functions around these trade-offs."
Full report:
https://www.kennasecurity.com/resources/prioritization-to-prediction-report-volume-five