Promon researchers have just exposed a StrandHogg 2.0 privileged boost vulnerability that affects lower versions of systems such as Android 9.0, and if exploited by hackers, all of a user's apps will be tainted by it.
Promon notified Google of the CVE-2020-0096 security breach, which the search giant has downgraded to a mark of "serious".
Thankfully, the loophole has not been widely exploited in the wild. But after today's disclosure, tens of millions of Android device users will become more vulnerable to attacks.

(From: Promon)
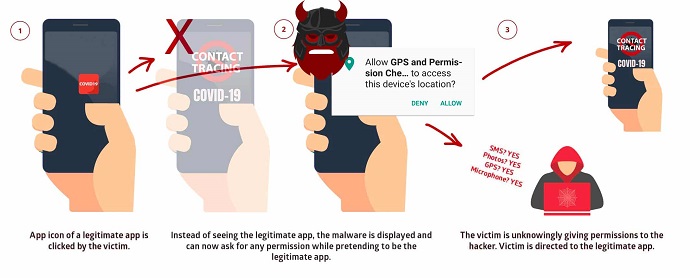
The Promon announcement states that the vulnerability allows malicious applications to gain a presumed legitimate identity while completely hiding themselves.
Once the malicious application is installed on the device, it can access the user's personal data, such as text messages, photos, login credentials, tracking GPS movements, call logging, and listening to the user via camera and microphone.
Promon said Google received a vulnerability disclosure notice on December 4, 2019, meaning the search giant had five months to patch the vulnerability before it was exposed to the public.
Vulnerability fixes for CVE-2020-0096 (covering Android 8.0 / 8.1 / 9.0) have been included in the April 2020 security patch for Android eco partners.
It should be noted that StrandHogg 2.0 is more complex than the first generation of vulnerabilities, making it harder to detect by anti-virus and security scanning programs.
End users need to be careful not to install Android apps from untrusted sources of unknown origin to avoid being affected by such malicious attacks.